Resources:
- Music Maker Featherwing Pinouts
- Forum: Interrupt troubleshooting
- Start Playing Issues
- General Issues
- Haunted Box Tutorial
- Internet Radio Tutorial
- Using LUA with the feather huzzah
Overview: This week I wanted to make a juke box that someone could interrupt with a particular song (in this case Smash Mouth’s Allstar). I set it up to run locally, and made a basic site out of Flask, with a button, that then changed the values on a API. I re-used some of my code from the Alexa Blender to to grab that changing API value. The issues I ran into were mostly w/ the feather’s music maker wing. It seems to be having issues maintaining its power when you use an interrupt based play back. I”m guessing there was something wrong w/ the interrupt calls as the blocking calls to the music still worked well. After doing a bunch of troubleshooting I couldn’t get the wing to be stable. I tried different iterations, and tutorials based on using Adafruit IO / doing streaming radio, changing pins and resistors, a different SD card, re-solder, etc. But the board would peter out after a bit. I even tried to follow something to re-flash the nodeMCU, thinking it might be a corrupted memory thing, but for some reason couldn’t make a proper connection. At least I found a lot of resources on music boxes / IoT music things.
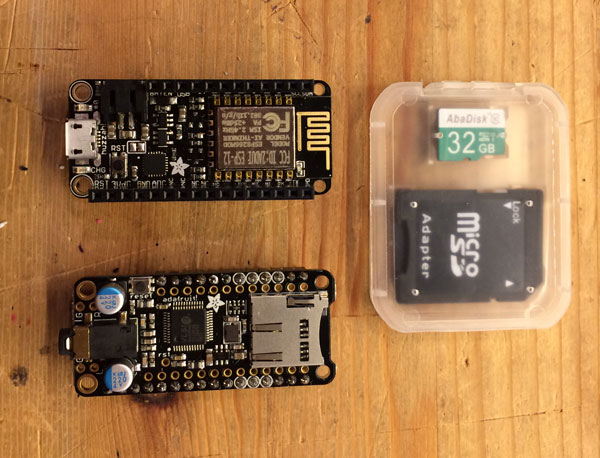
Components: Feather Huzzah, Music Maker Featherwing, Flask-Restful
Things I Experimented With: Timers, playlists, SD card.
Things I learned: Plug and play doesn’t really mean that.
Future Iterations: I’d probably set this up via a BaSS, and maybe use a different board. I’d like to still figure out what happened. As the user guide for the huzzah is pretty surface, but if you try and trouble shoot the NodeMCU there’s a rabbit hole of forums. I think as well, I need to find more robust ways of using a homebrew API.









